Coruna Jailbreak iOS Exploit Kit Compromises Thousands of iPhones
Coruna iOS Exploit has just been released for developers, and here is a guide on how to use Coruna jailbreak online and via the web.
The Coruna Jailbreak has recently gained attention across the iOS security and jailbreak communities. However, unlike traditional jailbreak tools released for public use, Coruna is an advanced iOS exploit framework discovered by security researchers.
This powerful toolkit includes multiple vulnerability chains that can target multiple iPhone models and iOS versions. While Coruna was originally designed for targeted cyber operations, its leaked code has now provided rare insight into how complex iOS exploits work.
In this article, we’ll explain what the Coruna Jailbreak is, how the exploit works, which iOS versions it affects, and why it’s important for the future of iOS jailbreak research.
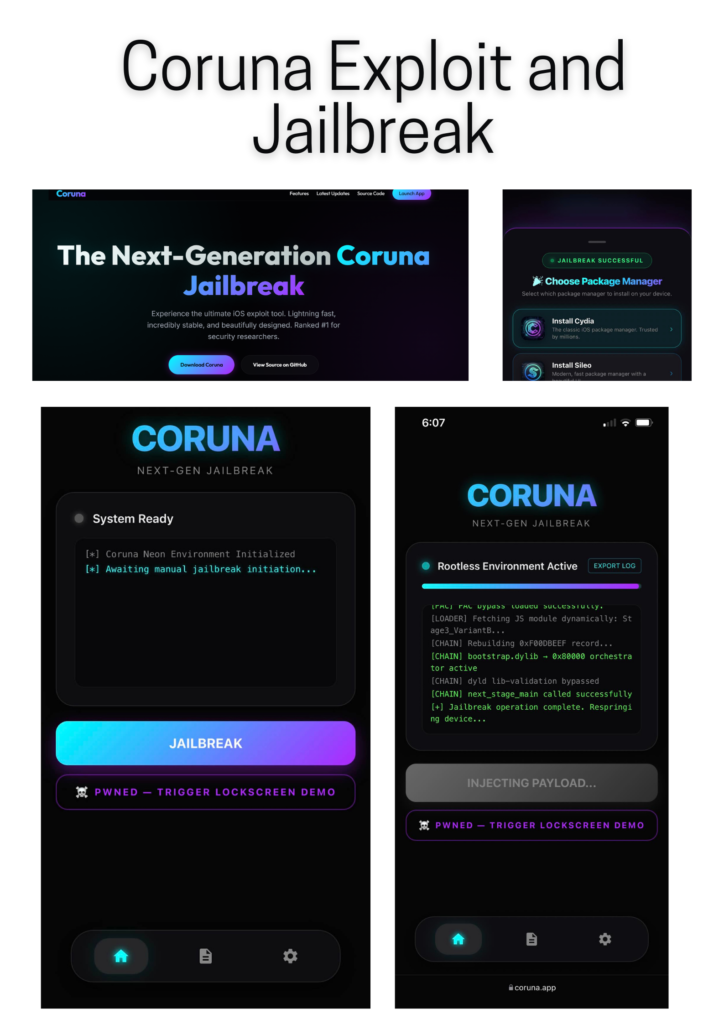
Coruna App
Experience the ultimate iOS exploit tool. Lightning fast, incredibly stable, and beautifully designed. Ranked #1 for security researchers. Important Fact: The core exploit was uncovered by Google’s Threat Intelligence Project. Free Open-Source Tool for Educational Purposes.
The Next-Generation Coruna Jailbreak download:
Coruna link 01:
Please click the button below to get the Corona jailbreak online.
Now, explore the game-changing features in the newest Coruna update, including expanded device compatibility
What is the Corona Jailbreak?
The Corona Jailbreak is an iOS exploit kit named after the Corona vulnerability, which contains a collection of vulnerabilities and exploit chains targeting Apple devices.
The toolkit was discovered after security researcher Duy Tran extracted parts of the code from a suspicious infrastructure website and uploaded it to GitHub for analysis. The repository does not include the final malware payload, but it does provide a rare glimpse of the internal architecture of a modern iOS exploit system.
The researchers discovered that the Corona framework contains 23 distinct vulnerabilities organized into five complete exploit chains. These chains collaborate to bypass multiple layers of Apple’s security architecture.
The framework is thought to have been developed with considerable resources, potentially costing millions of dollars in research and development. This level of sophistication indicates that the exploit kit may have originated from a government-level surveillance initiative or a professional cyber-espionage team.
Although the term Corona jailbreak is often used in online discussions, it is important to understand that Corona is not a publicly available jailbreak tool. Instead, it is a research-grade exploit framework that can gain deep access to iOS systems.
How the Coruna Exploit Framework Works
The Coruna Exploit Framework follows a multi-stage attack chain designed to bypass iOS security mechanisms. Each stage is carefully designed to escalate privileges until the attacker gains complete control over the device.
Device Identification and Fingerprinting
The first step in the Coruna attack chain is to identify the target device.
The exploit framework scans the incoming device to determine the following:
- iPhone model
- iOS version
- System architecture
- Browser environment
By gathering this information, the framework can select the correct exploit chain that matches the device configuration.
This dynamic targeting approach increases the success rate of the exploit and reduces the risk of detection.
Web-based entry point
Most Coruna attacks are initiated via malicious web pages.
Victims can unknowingly visit a compromised website that contains hidden scripts designed to trigger vulnerabilities in Apple’s WebKit browser engine, which powers Safari and many other iOS apps.
If the device is vulnerable, the exploit code is executed in the browser environment. From there, the attack attempts to escalate privileges beyond the browser sandbox.
This web-based delivery mechanism allows attackers to target devices without having to install any applications.
iOS versions affected by Coruna
The Coruna exploit framework targets a wide range of iOS versions, making it one of the most widespread iPhone exploit systems discovered in recent years.
Security analysis shows that Coruna can target the following:
iOS 13
iOS 14
iOS 15
iOS 16
iOS 17 to iOS 17.2.1
Since the exploit chains rely on specific vulnerabilities, many of them have been patched by Apple in subsequent updates.
Users running iOS 17.3 or later are generally protected from the vulnerabilities exploited by Coruna.
Apple frequently releases security patches that close these types of vulnerabilities, so keeping devices up to date is essential for security.
iOS Security Bypass
One of the most impressive features of the Coruna framework is its ability to bypass multiple iOS security protections. These protections are typically designed to prevent attackers from gaining full system access.
Coruna exploit chains include techniques to bypass:
- WebKit sandbox restrictions
- Kernel memory protection
- Pointer Verification Code (PAC) protection
- Application sandboxing
- Privilege escalation protections
- By combining multiple vulnerabilities into a single chain, Coruna can move from a simple browser exploit to a deep system-level approach.
Why the Corona leak is important
The Corona framework leak is extremely important for security researchers and jailbreak developers.
Understanding advanced iOS exploits
Apple’s operating system is considered one of the most secure mobile platforms in the world. Because of this, complete exploit chains targeting iOS are rarely made public.
The Corona leak gives researchers an opportunity to study how advanced exploit chains are built.
This insight can help security experts improve security technologies and identify future attacks.
Potential nation-state development
Experts analyzing the code believe that developing Corona would require a very large investment.
It would have taken a team of highly skilled engineers to create a toolkit with dozens of vulnerabilities, multiple exploit chains, and advanced security bypasses.
For this reason, some researchers believe that Coruna originated with government-level cyber operations or surveillance vendors.
This situation is similar to previous cyber weapons leaks, where tools originally designed for intelligence operations ended up in criminal enterprises.
Impact on Jailbreak Research
Although Coruna is not a jailbreak tool, the framework demonstrates several exploitation techniques that could inspire future jailbreak research.
Jailbreak developers often analyze vulnerabilities and exploit chains to better understand how Apple’s security system works.
Studying frameworks like Coruna can provide insight into:
- kernel vulnerability exploitation
- privilege insights
- sandbox escape strategies
- advanced memory manipulation
- These insights could ultimately influence the development of new jailbreak tools.
Coruna iOS 17 Sideload Bypass – Removing Apple’s 3-App Limit
Another important discovery related to the Coruna Jailbreak exploit framework is a potential way to bypass Apple’s three-app sideloading limit on certain versions of iOS 17.
Apple typically limits free Apple Developer accounts to installing only three sideloaded apps at a time. This limitation affects popular sideloading tools like AltStore, Sideloadly, SideStore, and other IPA installers.
However, recent research into the Coruna exploit chain suggests that this limitation can be bypassed by targeting a different system component within iOS.
Targeting the Install System Daemon
In previous iterations of the Coruna framework, researchers focused on injecting code into iOS’s main user interface process, SpringBoard.
But a new update to the Coruna research repository has changed the final stage of the exploit chain to target a different process called installd.
The install daemon is responsible for managing app installation on iOS devices. When a new app is installed, this system service performs several validation checks to ensure that the app is properly signed.
These checks include Apple’s security components:
AMFI (Apple Mobile File Integrity)
CoreTrust Signature Verification
If an app fails these checks, iOS immediately blocks the installation.
The Coruna exploit attempts to intercept this validation process at runtime, effectively changing how the system verifies apps during installation.
How Coruna Sideload Bypass Works (Research Concept)
The updated exploit chain introduces a new approach to manipulating the installation process.
Instead of injecting code into SpringBoard, the payload loads a custom dynamic library directly into the installation process.
Once the code is executed in this system service, iOS can modify the application validation logic before it performs its security checks.
This technique can allow:
Removing the three-app sideload limit
Installing unlimited apps using a free developer account
Installing tools like TrollStore on supported versions
Since the exploit runs in the same service responsible for monitoring installed apps, it sits directly in the enforcement layer used by Apple’s sideload restrictions.
Tools capable of modifying this service are extremely rare because they require deep system access.
TrollStore Installation Capability
Another interesting capability discovered during Coruna testing is the installation of TrollStore via the exploit chain.
The researchers suggest that plot may be able to launch TrollHelper, a component required for bootstrapping TrollStore installations.
However, this process may require simultaneous injection into SpringBoard to launch the helper correctly.
Another idea being explored is to replace a built-in iOS app (such as the Tips app) with an auto-launching installation assistant.
These experiments demonstrate how the Coruna exploit could lead to new installation methods for advanced iOS tools.
Why is this discovery important
The sideload bypass experiment demonstrates how powerful the Coruna exploit chain can be when combined with system-level injection techniques.
If the exploit becomes fully stable, it could enable several key capabilities:
- Unlimited side-loaded apps on vulnerable iOS versions
- New Safari-based installation methods
- Potential bootstrap tools for advanced tweaks
- New paths for modern jailbreak development
- However, the researchers emphasize that the Coruna framework is still under study and not ready for public use.
At the moment, the exploit remains a research project analyzing a leaked spyware toolkit, and the developers are still exploring its full capabilities.
The Future of Coruna and iOS Exploit Research
The Coruna discovery highlights the increasing sophistication of modern iOS exploit frameworks.
As Apple continues to strengthen its security architecture, attackers are being forced to develop more complex exploit chains that combine multiple vulnerabilities.
For security researchers, the Coruna leak provides valuable insight into how advanced iPhone exploit systems are designed.
At the same time, it reminds users that keeping devices up to date and following good security practices remain the best defense against modern cyberthreats.
Although Coruna is not a jailbreak tool, the techniques revealed in its framework could influence future research in both iOS security and jailbreak development. The Dopamine jailbreak suggests that the Coruna spyware chain could extend to iOS 17.
